Set Secure Credential activity
An activity that lets you change the settings of an access token for an external system for a process instance at runtime.

Configure the Set Secure Credential activity
To configure the Set Secure Credential activity, do the procedure in this topic.
Prerequisites
- When you configure this activity, the database type must be the same as access token specified in any database activities whose credentials you want to override.
- If you use a different database in the Set Secure Credentials activity than the one specified in the access token, the column names in both databases must be the same.
Good to Know
- To send an email notification, click
Advanced
 >
Email Notifications
>
Email Notifications  .
. For more information, refer to Email Notifications screen (Process Activities).
- To use this activity, you must have activities in this order:
Set Secure Credential activity > one or more activities for an external system, such as Database > Remove Secure Credential activity (optional)
- You must configure all settings for an access token in order to override it. You can not, for example, enter only a new user name and password.
- If you have more than one activity following a Set Secure Credentials activity that uses the same type of data source defined in the Set Secure Credentials activity, all of the access tokens for those activities will be overridden, even if they use different access tokens.
For example, in this process design, both the access tokens for two different databases, DB1 and DB2, would be overridden by the Set Secure Credentials activity:
Set Secure Credentials > Update Record (DB1) > Delete Record (DB2)
To avoid this problem, add a Remove Secure Credentials activity:
Set Secure Credentials > Update Record (DB1) > Remove Secure Credentials > Delete Record (DB2)
- In most text fields, you can use process data variables as an alternative to literal data values.
- This section shows the configuration settings on the configuration screens for this activity. Other configuration settings apply to system activities. For more information, refer to:
- You can configure whether this activity waits for other activities before it runs.
For more information, refer to How Do I Configure an Activity to Wait for Other Incoming Activities?
How to Start
- Open Process Builder.
For information about how to open this screen, refer to Process Builder.
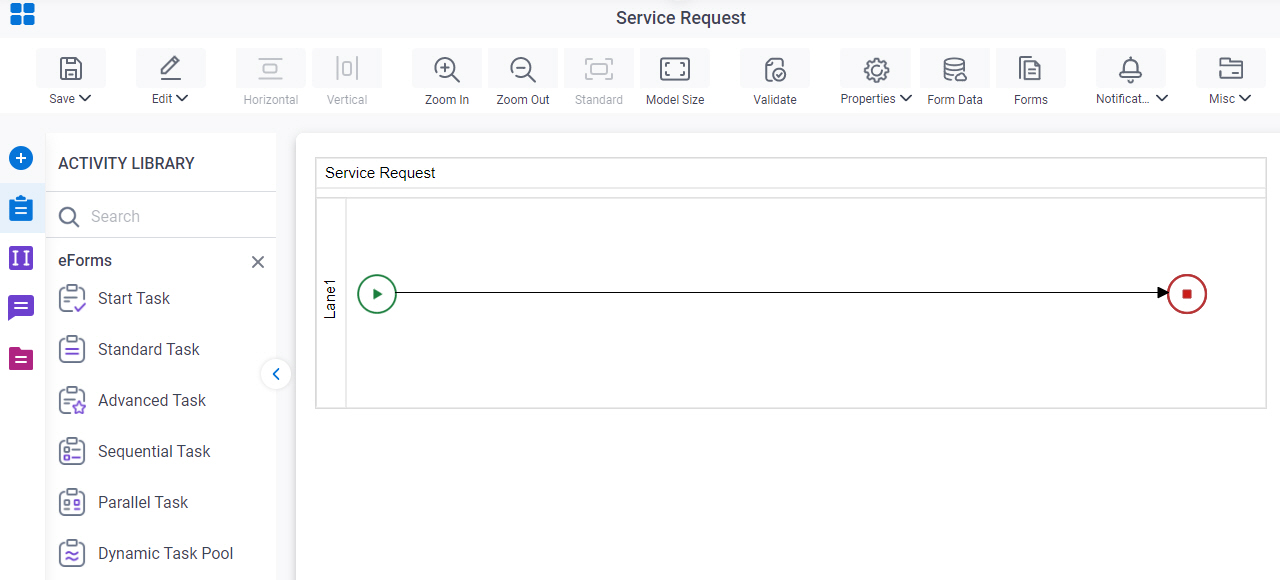
- In Process Builder, in the Activity Library,
open the AgilePoint NX tab.
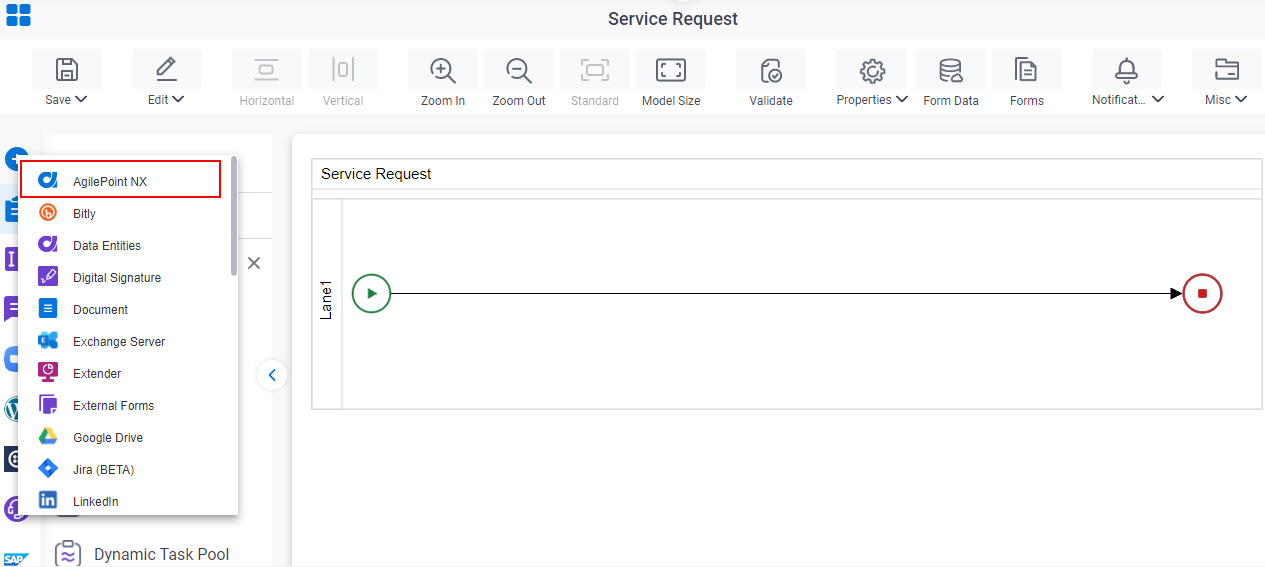
- On the AgilePoint NX
tab,
drag the Set Secure Credential
activity onto your process.
General Configuration
Specifies the basic settings for the Set Secure Credential activity.
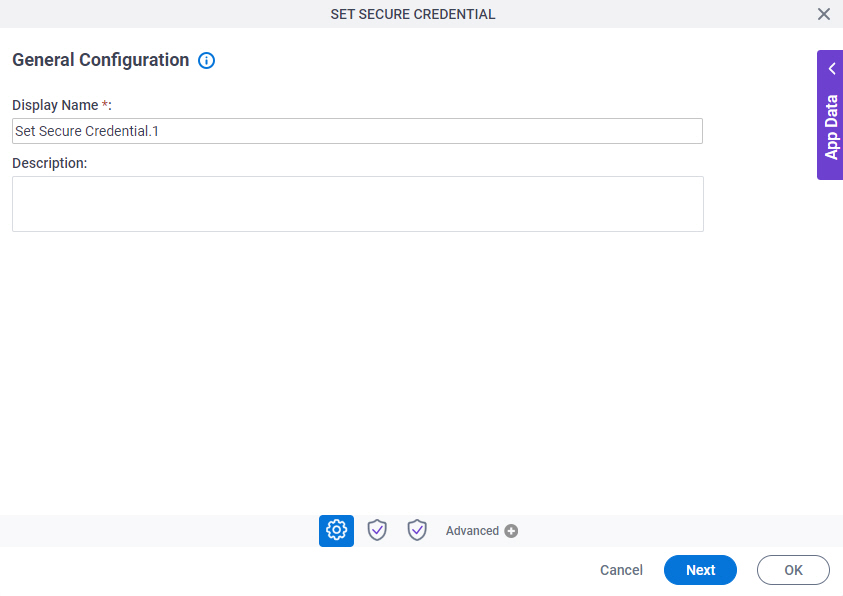
Good to Know
- Documentation for this screen is provided for completeness. The fields are mostly self-explanatory.
Fields
| Field Name | Definition |
|---|---|
|
Display Name |
|
|
Description |
|
Secure Credential Types
Specifies the external system type for which to change the settings for the access token at runtime.
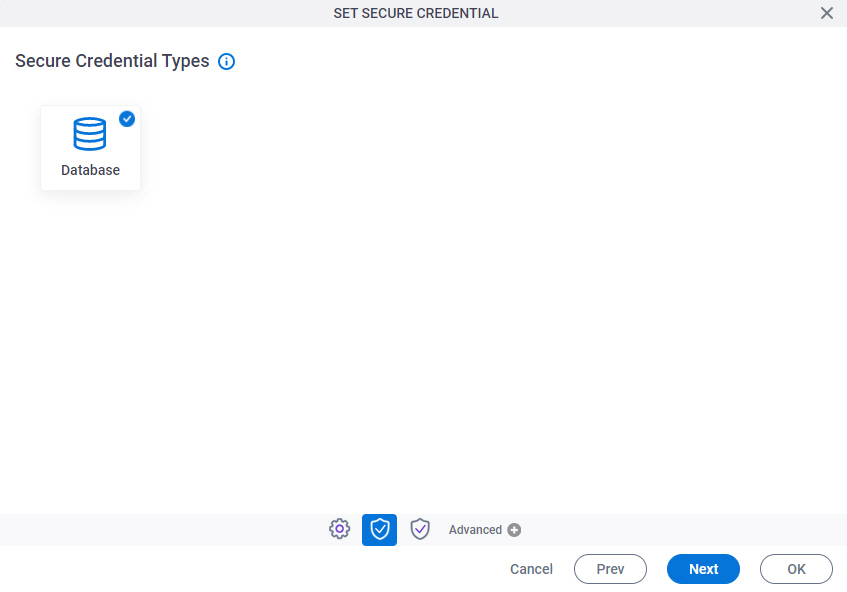
Fields
| Field Name | Definition |
|---|---|
|
Database |
|
Set Secure Credential Configuration (Database)
Specifies the information to change the settings for the database access token.

Fields
| Field Name | Definition |
|---|---|
|
Database Type |
|
|
Database Server Name |
|
|
Database Name |
|
|
Port |
|
|
Timeout(seconds) |
|
|
SSPI (Integrated Security) |
|
|
User Name |
|
|
Password |
|