Access Token for Anonymous Forms
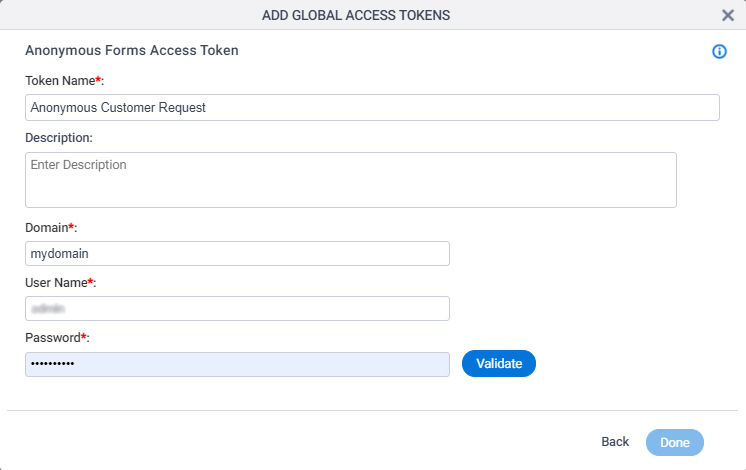
Configure an access token to connect to an anonymous form. This type of access token provides credentials that let non-authenticated users complete an eForm in AgilePoint NX.
Background and Setup
Examples
- (Example) Use Anonymous Authentication in a Form-Based App
- (Example) Use Anonymous Authentication in a Process-Based App
- Examples - Step-by-step use case examples, information about what types of examples are provided in the AgilePoint NX Product Documentation, and other resources where you can find more examples.
Prerequisites
- Account credentials for anonymous authentication. This is the account the eForm uses to connect to AgilePoint NX, and get and submit data in the app. You can use an
AgilePoint NX account
or an account in
Active Directory.
If you do not use any of these authentication methods in your organization, you can create an AgilePoint NX account to use for anonymous authentication.
Active Directory authentication is not available for AgilePoint NX OnDemand.
- As a security best practice, in your access token for anonymous forms, AgilePoint recommends using a user with minimum access rights. This is a user with the Users role with the default access rights.
- An app designer who configures an eForm to use anonymous authentication (used with anonymous forms) must have a role with the Allow Enabling Anonymous Access
access right.
The Allow Enabling Anonymous Access role lets the application designer create an anonymous form in App Builder at design time. It does not control the security for the anonymous form or the anonymous form user at runtime. The user credentials used for the anonymous authentication access token do not require this access right.
Good to Know
- To enforce strict security, AgilePoint highly recommends you use anonymous forms for data entry only, and avoid using lookups that connect to your backend systems.
However, the decision whether to use lookups in anonymous forms is based on your business requirements. If your requires you to use a lookup to backend system, make that design choice as necessary.
- Optionally, in AgilePoint NX OnPremises and AgilePoint NX Private Cloud, anonymous forms can use the AgilePoint Service Account for authentication if you select User System Account when you configure an access token for anonymous forms. However, this practice carries security risks. It is not recommended unless you have a specific business requirement for Service Account access, and the security risks are mitigated.
If you use the AgilePoint Service Account, the credentials are not stored in the database.
- If you have questions about the security impacts or best practices for anonymous forms, contact AgilePoint Professional Services.
- In most cases, you can use a global access token or
an app level access token:
- Global access tokens are shared across all users and apps. If you want all process designers and runtime app users in your AgilePoint NX tenant to be able to connect to an external data source, use a global access token. An example is a SharePoint site on an intranet that all employees in a company can access.
- Application level access tokens are shared with all processes in a process-based app, or restricted to use within a form-based app. Use application level access tokens if only process designers or runtime app users for a particular application should access an external system — for example, a Box account that is only used to share files within a small team.
- Access tokens are collections of credentials that are used to authenticate communication directly between AgilePoint NX and an external system. Because it is the AgilePoint NX system that uses these credentials, rather than an app, there is no difference between
design time
and
runtime
access tokens. Access tokens are never checked in or published, and they do not use version control. If you change an access token in the App Builder or Manage Center, the access token changes immediately everywhere the access token is used. Changes to app level access tokens apply to all versions of an app, including running application instances. Changes to global access tokens apply everywhere they are used in AgilePoint NX. You can not roll back an access token to a previous version.
For more information, refer to What Data Is Deleted When I Delete an App or Application Resource?
- This screen may look different in different places. The UI varies for this screen depending upon how you open it. However, the fields for this screen are the same in all places.
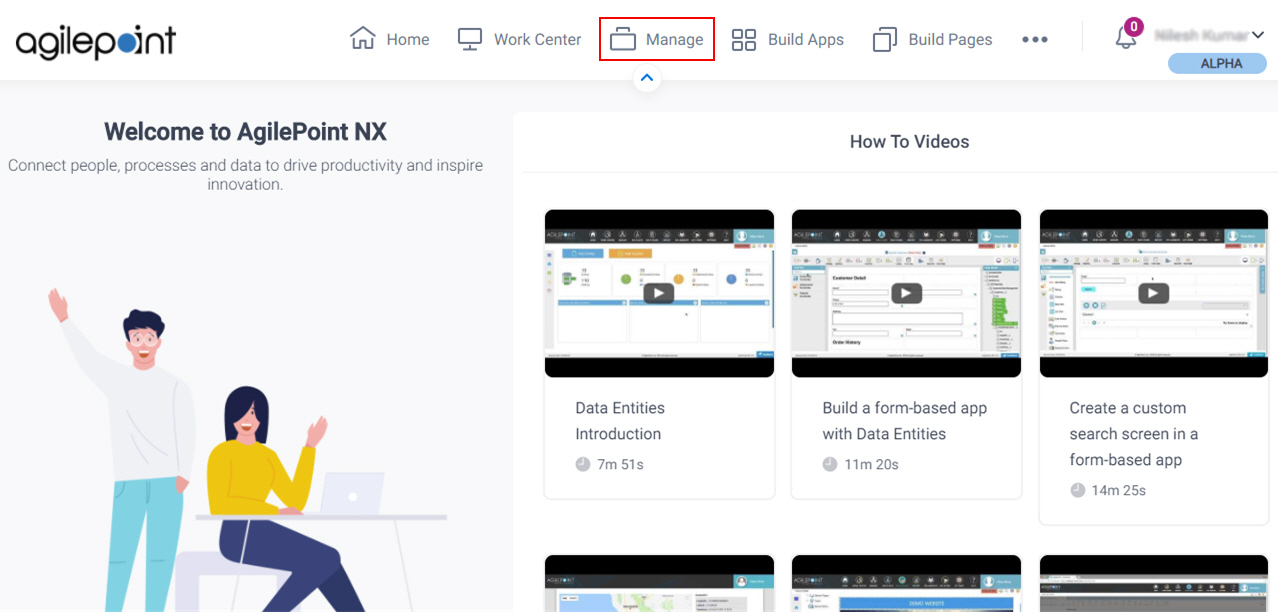
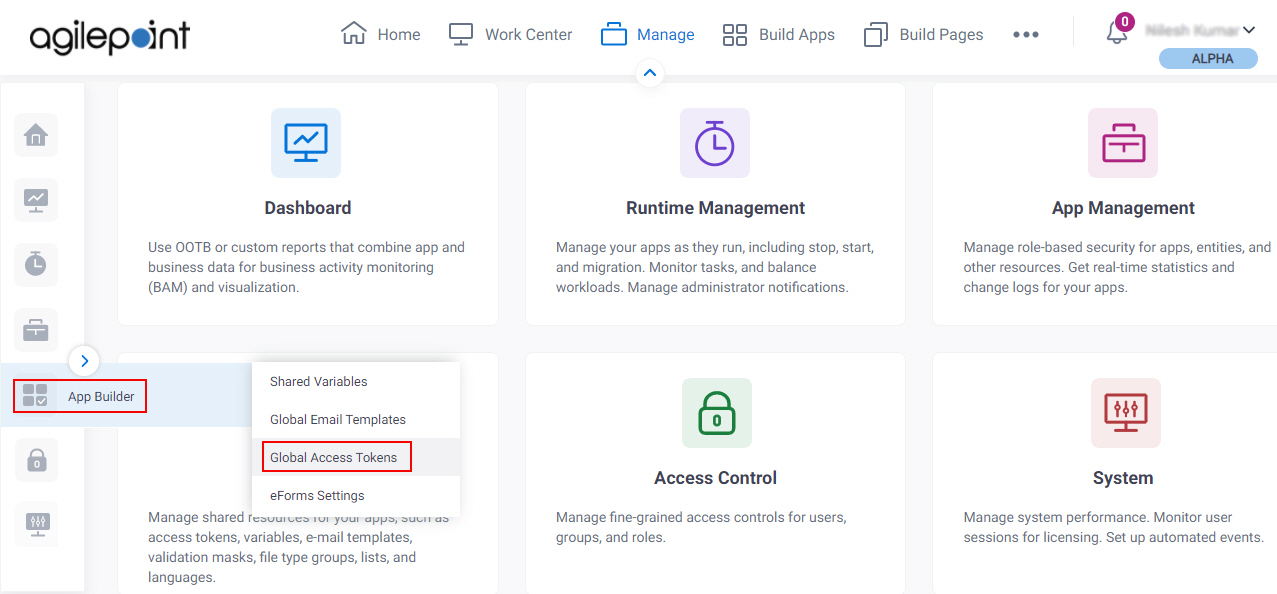
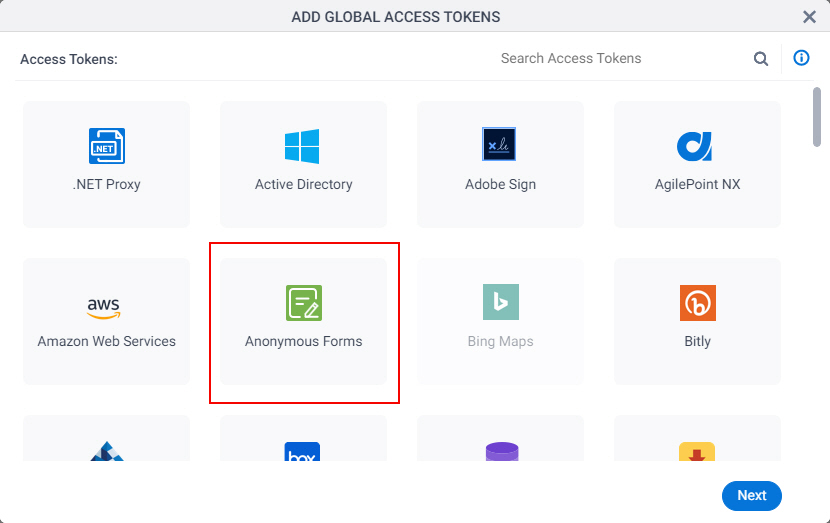
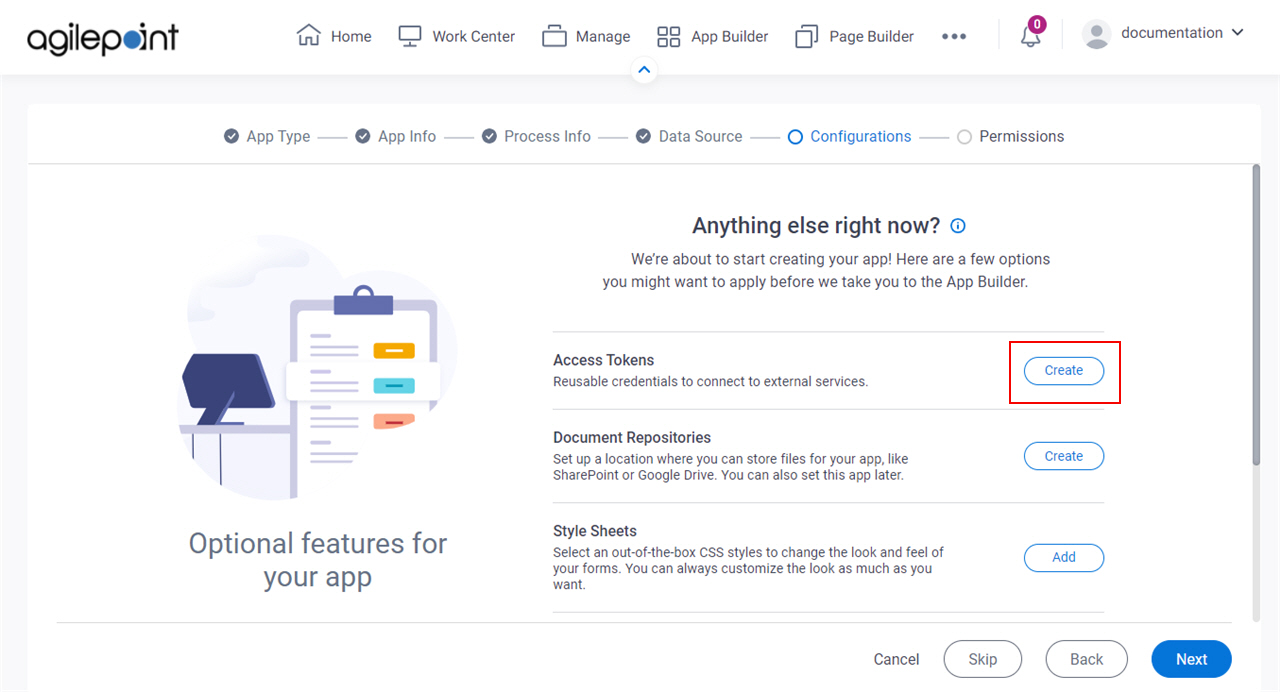
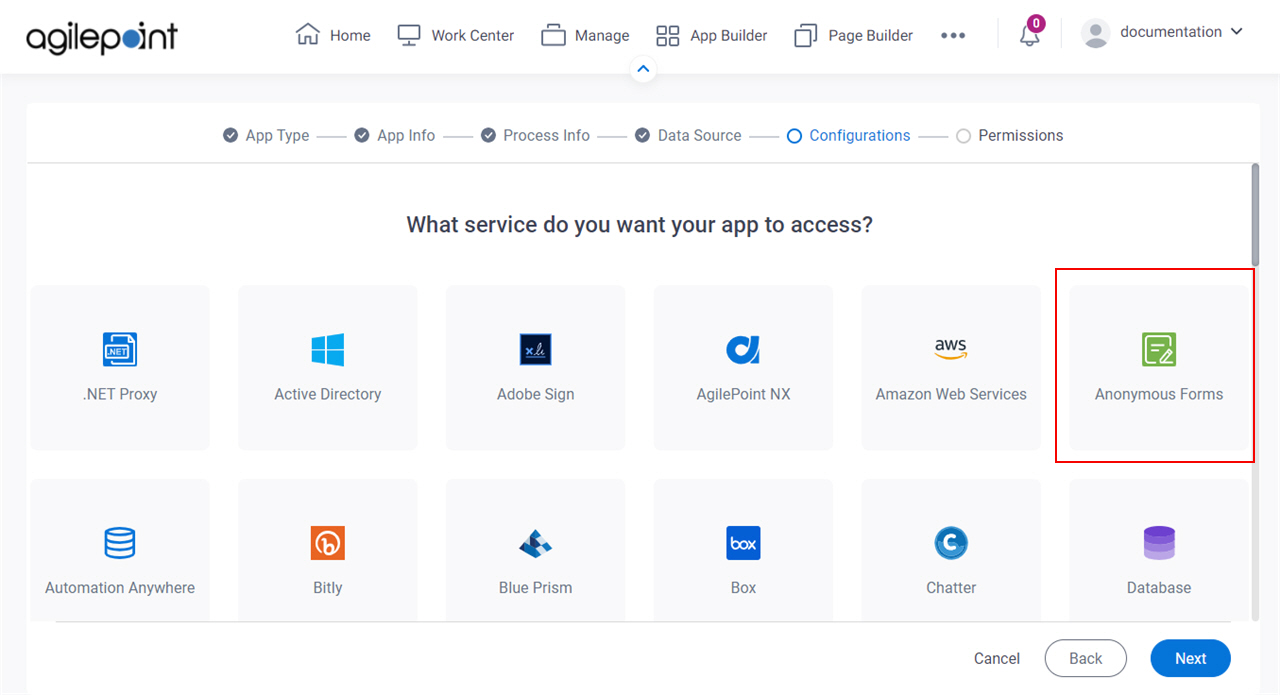
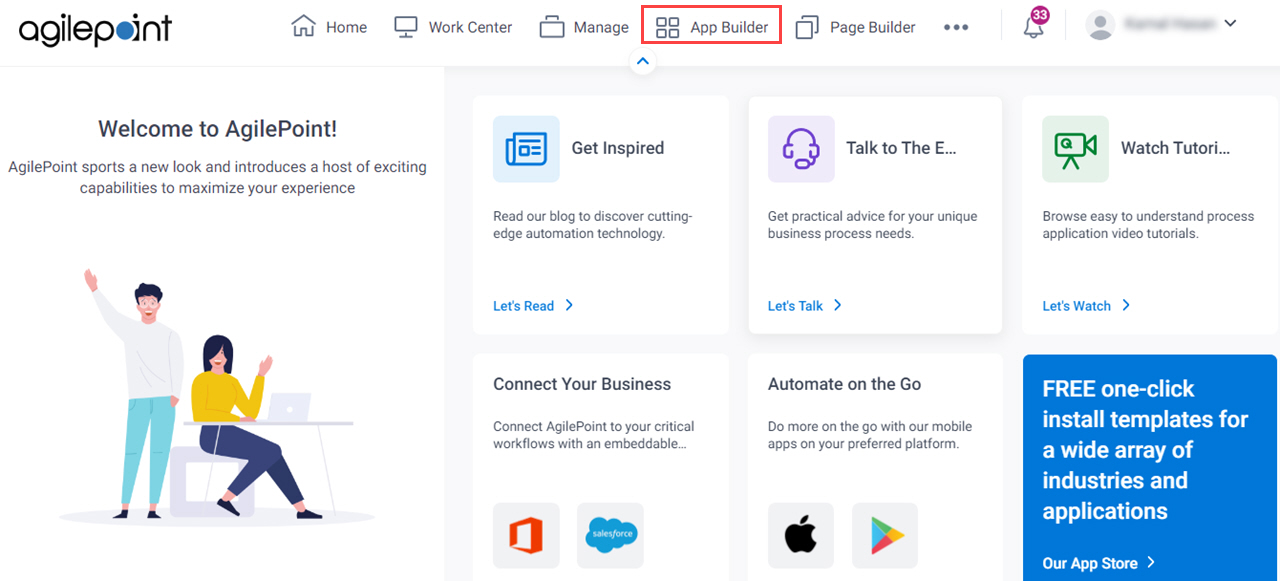
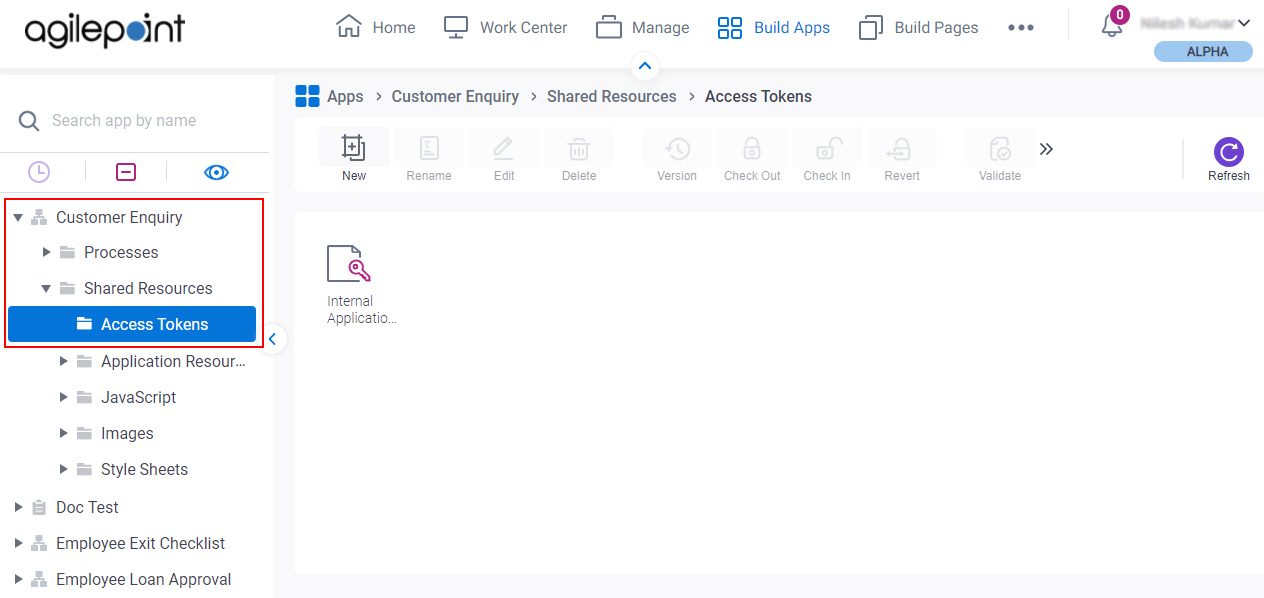
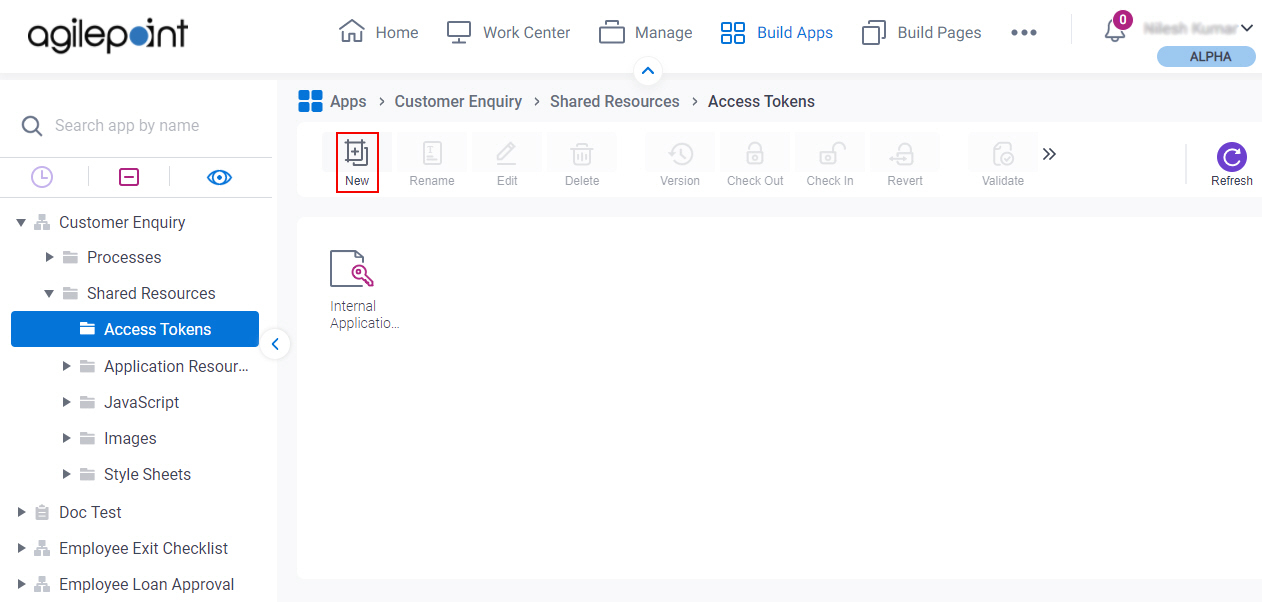
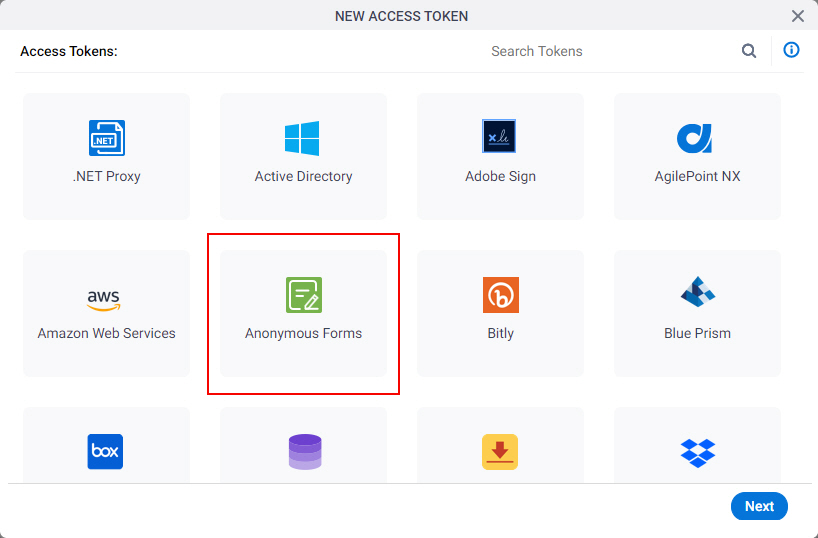
How to Start
Fields
| Field Name | Definition |
|---|---|
|
Token Name |
|
Description |
|
|
Domain |
|
|
User Name |
|
|
Password |
|
|
User System Account |
|
|
Validate |
|
Encrypt |
|